
The People’s Liberation Army may have been funding a massive group of Chinese hackers since 2006, according to a 74-page report by the US-based security firm Mandiant. Reading like the backpage of a Michael Crichton novel, the report details how a large hacking group, APT1, based in the Pudong district of Shanghai has been responsible for hundreds of cyber attacks in the last seven years.
87 percent of APT1’s hacking victims were based in English-speaking countries, according to the report, and include “development agencies, foreign governments in which English is one of multiple official languages, and multinational conglomerates that primarily conduct their business in English.”
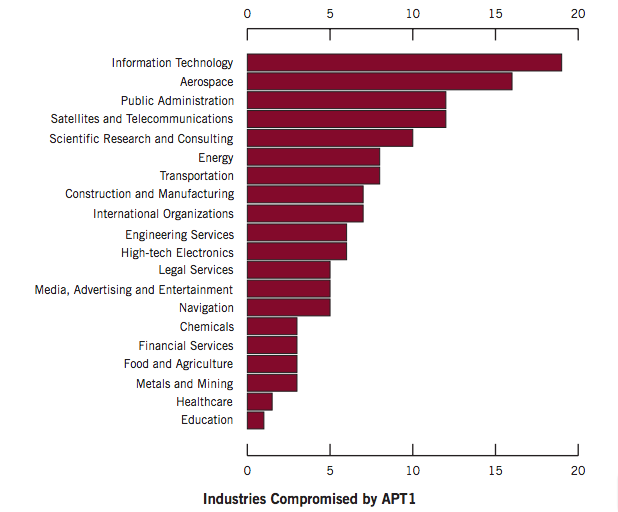
We believe that organizations in all industries related to China’s strategic priorities are potential targets of APT1’s comprehensive cyber espionage campaign. While we have certainly seen the group target some industries more heavily than others (see Figure 13), our observations confirm that APT1 has targeted at least four of the seven strategic emerging industries that China identified in its 12th Five Year Plan.
APT1 also has many suspicious structural similarities to a PLA unit. Mandiant believes APT1’s offices are located in a 12-story building fitted out by China Telecom and employs hundreds to thousands of employees, while “PLA Unit 61398 is also located in precisely the same area from which APT1 activity appears to originate.”
For its part, China/PLA has denied the allegations, the Washington Post reports.
The Mandiant report goes into the nitty-gritty of the hacking process, but the takeaway is really this: never, ever open a strange attachment. Ever.














































哦,不是蓝翔大技校作孽啦?!